- Sản phẩm & Dịch vụSản phẩm & Dịch vụ
- Giải phápGiải pháp
- Bảng giáBảng giá
- Công tyCông ty
- Tài liệuTài liệu
vi
vi
Trung Nguyen

| CyStack Advisory ID | CSA-2019-03 |
|---|---|
| CVE IDs | CVE-2019-16057 |
| Severity | Critical |
| CVSS v2 Base | 10.0 |
| Vendor’s announcement | Link |
CyStack Security discovered a remote code execution vulnerability in the D-Link DNS-320 ShareCenter device which its version is lower or equal 2.05.B10 . By exploiting the vulnerability, a remote, unauthenticated attacker can access to all application commands with root permission. This device is a popular network storage device and interestingly, in the past, it was also reported that it contains a backdoor itself.
While doing some research on network devices we found a command injection vulnerability at the login module of a D-Link DNS-320 device. The flaw exists at a hidden feature called SSL Login which its required parameter, port, can be poisoned.
In this article, I will show how we found out the flaw and analyze what happened in the old version of the firmware.
Firstly, we download the firmware
$ mkdir /tmp/dns_320 && cd mkdir /tmp/dns_320
$ wget ftp://ftp2.dlink.com/SECURITY_ADVISEMENTS/DNS-320/DNS-320_REVA_FIRMWARE_PATCH_2.05.B10.ZIP
$ unzip DNS-320_REVA_FIRMWARE_PATCH_2.05.B10.ZIPNext, we use Binwalk and Firmware Modification Kit to extract it
# If you do not have these tools, install them first
$ sudo apt-get install git build-essential zlib1g-dev liblzma-dev bsdmainutils python
$ wget https://storage.googleapis.com/google-code-archive-downloads/v2/code.google.com/firmware-mod-kit/fmk_099.tar.gz
$ tar -xvf fmk_099.tar.gz fmk/
$ cd fmk/src/others/ && make && cd -
$ curl "https://bootstrap.pypa.io/get-pip.py" -o "get-pip.py"
$ python3 get-pip.py
$ git clone https://github.com/ReFirmLabs/binwalk.git && cd binwalk && python3 setup.py install && cd -
$ binwalk -eM DLINK_DNS320.2.05b10\(2.13.0226.2016\)
$ ./fmk/unsquashfs_all.sh _DLINK_DNS320.2.05b10\(2.13.0226.2016\).extracted/3F5020.squashfs
# All binaries are now in the following folder
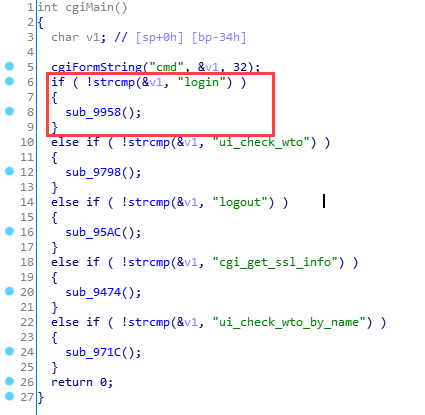
$ cd squashfs-root/Our target binary is /cgi/login_mgr.cgi which handles login requests. We focus on function cgiMain()
Firstly, if the parameter cmd equals "login" then sub_9958 will be called
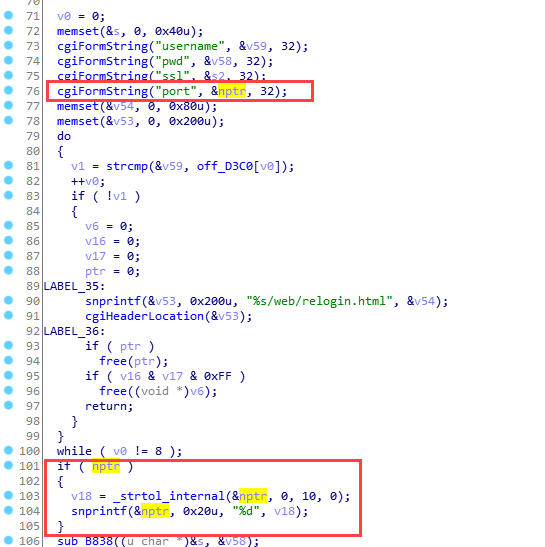
sub_9924() will be called with parameter port
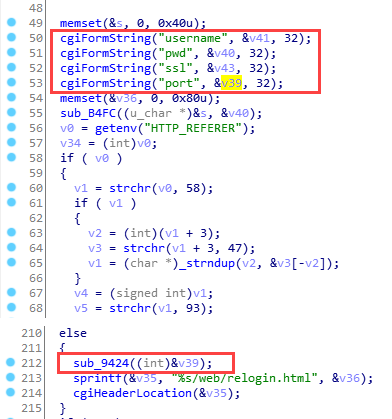
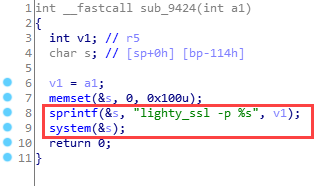
Let’s take a look at sub_9924(). We can see that if an attacker controls parameter v1 which stands for port, he will be able to arbitrarily execute commands, which is the key point in this vulnerability
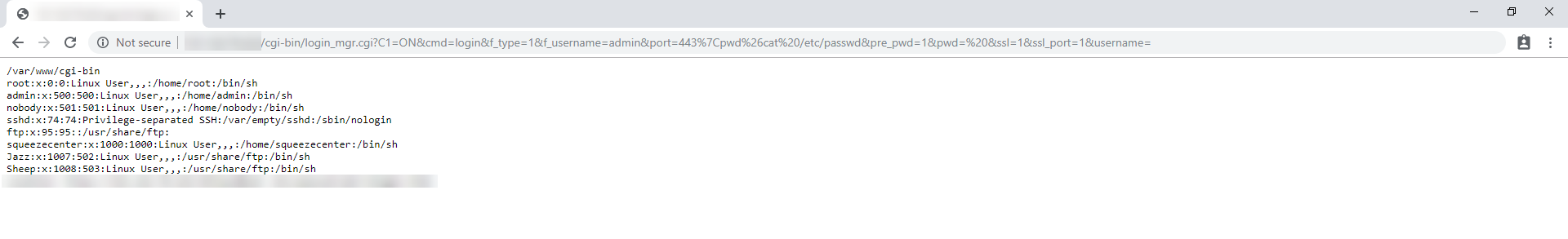
By poisoning the parameter port, we can perform an RCE attack like below
D-Link team released a patch for this issue on 11/04/2019. According to their release notes, the patch is for login_mgr.cgi allows attackers pipe commands to the user.log. I don’t know exactly what issue they found related to the flaw I’m addressing in this article, but the patch worked. They fixed it by type casting parameter port to Integer.
Reading Time: 2 minutes CyStack Advisory ID CSA-2025-01 CVE IDs CVE-2025-59837 Severity High CVSS v3 Base 7.2 Recently, I analyzed a security […]
Reading Time: 2 minutesCyStack Advisory ID CSA-2022-01 CVE IDs CVE-2022-41938 Severity Critical CVSS v3 Base 9.0 Synopsis CyStack’s researchers recently discovered a Stored […]
Reading Time: 3 minutesCyStack Advisory ID CSA-2021-01 CVE IDs CVE-2021-44832 Severity Critical CVSS v3 Base 10.0 Synopsis Cyclos is a payment software created […]