- Products & ServicesProducts & Services
- SolutionsSolutions
- PricingPricing
- CompanyCompany
- ResourcesResources
en
en
Winston To
TL;DR

Cyber threat intelligence is the examination of the organization’s cybers threats | Source: ImmuniWeb
Threat intelligence is the practice of collecting, processing and assessing data to identify and understand cyberattacks. The collected data will then be refined and organized in order to deal with cyber threats.
The purpose of threat intelligence is to have an overview of risks from external sources. Threat intelligence provides in-depth data and context about suspicious sources of threats, their capabilities, and the indicators of compromise (IoCs). With this kind of information, organizations can actively protect themselves when there is an event of cyberattack.
Threat intelligence is a powerful practice for any organization because it can help you to:
Indicators of Compromise (IoCs) provide data regarding a cyber attack, including the consequences of the attack and its sources. Threat intelligence can use IoCs to map cyber attacks with known threat details and activities. These are the most common types of IoCs:
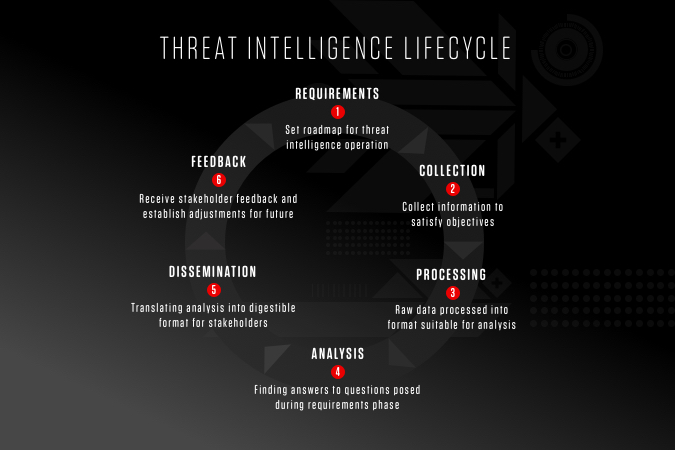
6 steps of threat intelligence cycle | Source: Crowdstrike
The threat intelligence lifecycle is a full process of collecting raw data and turning it into insightful security intelligence. The 6 stages make the process of threat intelligence become more refined and efficient over time.
This is considered one of the most important steps because it sets the objectives, roadmap, direction, and everything an organization needs for its threat intelligence. During this stage, the team can discover the following factors:
2. Collection
After the first step, the team can figure out ways to collect the data to fulfill the requirements. The information can be retrieved and gathered from multiple sources, such as:
3. Processing
After the raw data has been collected, you need to sort, clean, and organize the data. Following the previous step, the data will need to be transformed into a suitable format for cybersecurity analysis.
4. Analysis
After having the processed data, the team must conduct a thorough analysis to fulfill the requirements in the first step. The analysis should provide actionable insights and valuable recommendations for the stakeholders to investigate and mitigate the attacks.
5. Dissemination
In this stage, the threat intelligence is delivered to end users or to a security tool which uses the data to identify and defend against threats. Besides the analysis is also presented to stakeholders in the form of reports, alerts, or data files.
6. Feedback
The feedback stage involves gathering reviews and feedback from the stakeholders to assess the effectiveness of the threat intelligence. This feedback can be a valuable source to decide how threat intelligence should be improved in the future.
There are 4 levels of threat intelligence. Each level requires a different context, analysis, stakeholders, and investment costs.
This level of intelligence focuses on the near future and identifies simple IoCs. Simple IoCs can be bad IP addresses, unusual traffic and requests, and malicious domain names,… Tactical threat intelligence is the most straightforward kind of intelligence and is usually automated. It has a short lifespan because IoCs, such as bad IP addresses, can become obsolete quickly.
Tactical intelligence is technical in nature, so the stakeholders are usually people who work at the forefront of the IT team, including:
Technical threat intelligence provides details on signs indicating a cyberattack is taking place. Indicators of Compromise will be monitored closely with AI tools to detect the cyberattacks timely. Technical intelligence plays a vital role in detecting and mitigating social engineering attacks. Moreover, this type of intelligence can be updated quickly to track the attackers’ tactics.
Operational threat intelligence studies all the aspects in regard to the adversaries. This level of intelligence provides the ”who”, ”why”, “when”, and “how” of the cyberattacks. The “who” is the profile and the source of the attack. The “why” refers to the motives or the purpose of the attack. The “when” is the timing of the attack. The “how” is made up of the tactics, techniques, and procedures (TTPs) of the attacker.
Operational threat intelligence requires more effort and resources to build than tactical intelligence and has a longer lifespan. The reason for this is attackers can’t change their TTPs as easily and quickly as they change their tools (for example, a type of malware).
Operational threat intelligence can serve as a reliable and valuable information source for:
Strategic threat intelligence outlines an overview of a company’s threat landscape. This type of intelligence analyses potential cyberattacks and possible consequences for high-level and non-technical decision makers in an organization. Strategic intelligence is the most complex intelligence compared to the types mentioned above since it requires more expertise in broader areas such as sociopolitical and business concepts.
An excellent strategic intelligence should provide insights into risks, movements in threat actor tactics and targets, and geopolitical trends in order for high-level executives to make wise cybersecurity investments that effectively protect the organization’s systems. Strategic intelligence is often presented in a report or research format.
Stakeholders find strategic threat intelligence useful can include:
Threat intelligence provides insights into the threat source, tactics, techniques and procedures, which help the organization to proactively take security measures to detect and block cyberattacks. A thorough threat intelligence system can save a business thousands of dollars by not compensating for operational disruptions and cyberattacks.
Reference
https://www.crowdstrike.com/cybersecurity-101/threat-intelligence/
https://www.kaspersky.com/resource-center/definitions/threat-intelligence
https://www.recordedfuture.com/threat-intelligence
https://www.vmware.com/topics/glossary/content/threat-intelligence.html
Reading Time: 5 minutesWhat Is Penetration Testing? Image by ra2 studio on Shutterstock Penetration testing (pen testing) is a simulated and authorized attack […]

Reading Time: 4 minutesHow to Secure Your Cloud Environment: Best Practices and Strategies Image by macrovector on Freepik Businesses are migrating from on-premises […]
Reading Time: 4 minutesData Privacy in the Workplace: Balancing Employee Privacy and Business Needs Image by VideoFlow on Shutterstock No employee wants to […]