Do not wait for the hackers to exploit the vulnerabilities of your software; then, you have to make extra efforts to fix the damages. Instead, your development team must try initiating attacks on the system(s) to spot potential vulnerabilities beforehand. This process is called a penetration test or pentest – our topic today.
In this article, we further explain this testing practice – from the view of experts with over ten years of providing pentest services for clients worldwide and reveal when to do a pentest.
You will not afford to miss it!
What Is a Pentest?

Penetration testing is different from normal testing.
Imagine the testers as ethical hackers who make serious attempts to enter your software applications from networks, servers, mobile devices, web applications, etc. It can be done manually or automatically with penetration testing tools. This way, they can detect vulnerable entry points that hackers might exploit later and inform the development team to seal the gaps.
Once the testers detect a vulnerability, they will utilize the compromises to launch subsequent exploits and get deeper access to internal sources.
Besides finding potential weaknesses, a pentest helps assess your business’s readiness for cyberattacks and, at the same time, provides critical crisis training for employees on how to react and overcome penetrating exploitations effectively.
In the long term, penetration testing reduces the chances of hacking and data breaches, which saves your business money and maintains goodwill among stakeholders.
When to Do a Pentest?

Although a pentest is critical for almost all software, it requires effort and expertise to complete. Not to mention, too early penetration testing is not recommended. You waste money to do the pentest again if new codes are not tested.
Thus, developers and companies just need to apply this type of testing in specific situations.
Undergo a merger or acquisition
The M&A process is not work done overnight. A large amount of data and digital assets will be gathered, reviewed, and merged. And security is a big problem involving data transfer and exchanges. Any breaches or leakages can negatively affect finances and the bottom line of both your business and stakeholders, which is never expected.
With this in mind, more and more merger and acquisition deals involve cybersecurity as a due diligence part – confirmed by Forbes. Accordingly, penetration testing should be carried out both before and after any merger or acquisition in order to safeguard the crucial data of both organizations.
Add network infrastructure or application(s)
Your business needs to install a new network or application sometimes. It is when to do the pentest!
While they make your operation and management easier, the network and applications present security challenges. They rely on different connected endpoints – possibly vulnerable under penetration attempts. Businesses need to test the network and applications before putting them into use.
The simplest way to use scanning tools such as network scanners, port scanners, and vulnerability scanners is to test the network baseline. This process provides more information about the network or entry points of the applications and existing flaws.
Next, the tester will simulate a user with access and elevated privileges to attack the vulnerable entries of the network or application. This is internal penetration testing. Also, the tester performs as a tech-savvy user who makes attempts to access the architecture documentation and the source code of the network or application. This kind of pentest is the most difficult.
Complete the functions of a new application

Penetration testing is also applied for application implementation.
However, we only suggest it when your app is fully functional and almost production-ready. This means all the features intended for release are done and verified by traditional testing. As mentioned earlier, new codes added might be involved in the security of the app, yet they are vulnerable to attacks.
Conversely, development teams also avoid applying a pentest after the application is live. The testing process can bring the app down and interrupts the user experience. It is always better for the testers to hammer away at the application before it is released. In addition, launching an application without doing a pentest means allowing malicious hackers to exploit the vulnerabilities and cause nerve harm.
Apply new security patches
While security patches are supposed to fix bugs and enhance vulnerabilities of the application, they are also beneficial for hacking attempts. Attackers can read the patches and come up with ideas to breach them since the patches are publicly available.
For this reason, businesses must verify security patches using a security-focused approach, such as doing a pentest before launching them to the entire IT environment.
Update end-user policies
Modifications in end-user and corporate policies may lead to logical flaws and vulnerabilities that are not picked up by scanning tools or basic vulnerability assessments.
Pentest must find such configuration errors and logical shortcomings by providing a profound understanding of the newly established information security systems.
How Often Should You Do a Pen Test?
Now you already know when to do a pentest. The next question is the ideal frequency.
First and foremost, penetration testing on a regular basis will allow a more consistent network and IT security management.
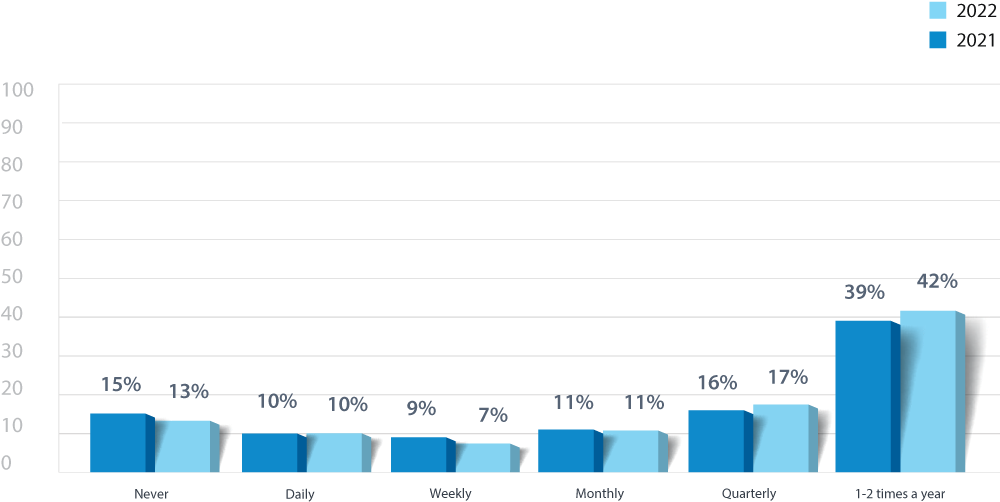
Secondly, most cybersecurity experts apply penetration re-testing once or twice per year. It helps balance all resources: time, talents, and budget. We agree with that frequency and also recommend running the vulnerability scanning tools daily.
In addition, it is better to hire a professional pentest service than do it in-house. Remember that penetration efforts involve both IT and non-IT knowledge; thus, you can be at ease when leveraging innovative methods and best practices in the sector used by third-party security professionals. In addition, outsourcing saves costs on hiring full-time penetration testers, training them, and sponsoring them for certifications.
Don’t know where to hire experts? – Check CyStack’s Pentest Services.
The professionals at CyStack have more than ten years of combined experience in cybersecurity across a range of industries, including finance, e-commerce, and SaaS. So far, we have helped detect many serve CVEs and Zero-day vulnerabilities on giant technology platforms such as Microsoft Azure, D-Link, Cesanta Mongoose, Cyclos, etc. and have been honored by leading corporations: Microsoft, Deloitte, HP, Dell, etc.
Why choose CyStack’s pentest services:
- Optimal Crowdsourced Penetration Testing solution that is seven times more effective
- Compliance with international standards: PCI-DSS, ISO27001, HIPAA, SOC 2
- Real-time and continuous reports to facilitate early detection and remediation
- Guarantee of 100% vulnerabilities eliminated.
Final Words
Drop us a line for expert consultation to discuss further and draft a particular pentest plan.
Then, even if you do not intend to choose CyStack’s pentest services, it is still important to take notes on when to do a pentest and have a strategic plan to secure your business and networks!
 5 minutes read
5 minutes read
